A Squid Proxy Server is a feature-rich web server application that provides both reverse proxy services and caching options for websites. This provides a noticeable speedup of sites and allows for reduced load times when being utilized.
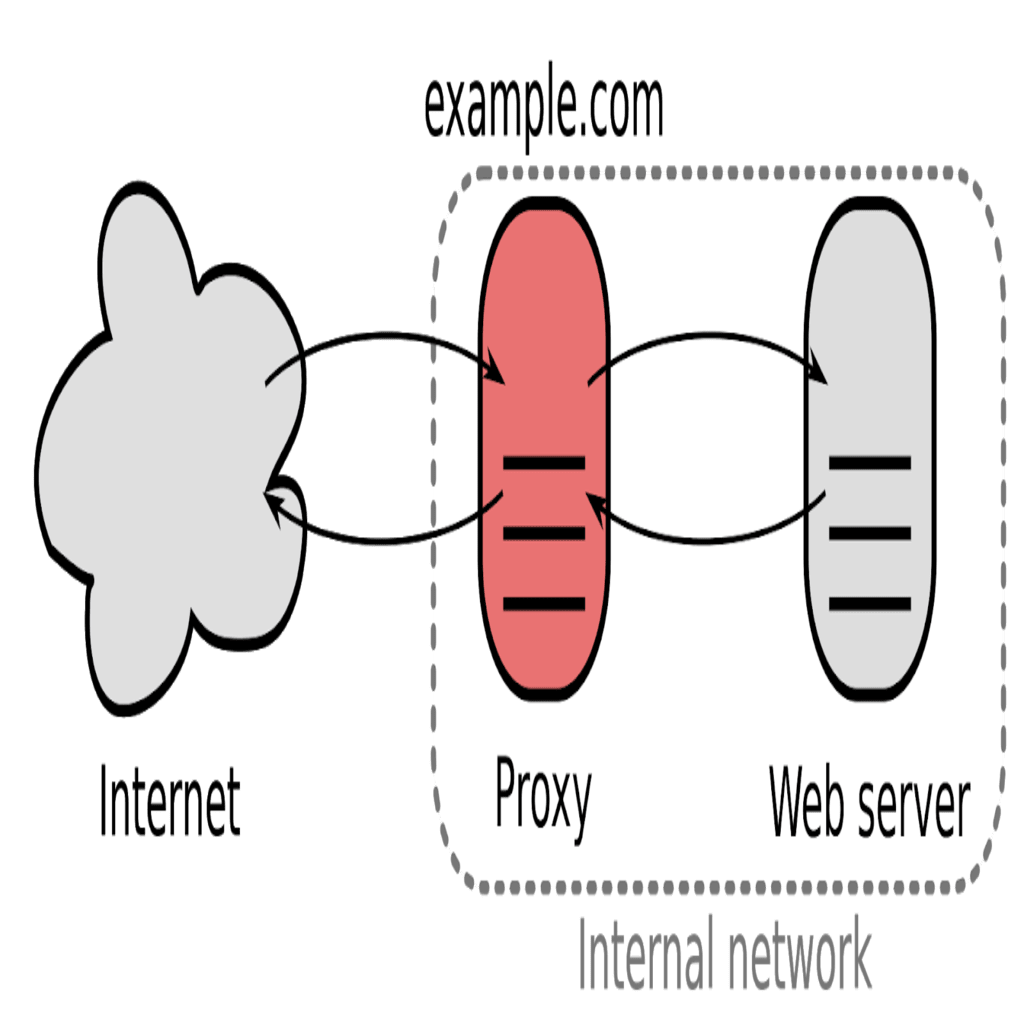
Squids reverse proxy is a service that sits between the Internet and the webserver (usually within a private network) that redirects inbound client requests to a server where data is stored for easier retrieval. If the caching server (proxy) does not have the cached data, it then forwards the request on to the web server where the data is actually stored. This type of caching allows for the collection of data and reproducing the original data values stored in a different location to provide for easier access.
A reverse proxy typically provides an additional layer of control to smooth the flow of inbound network traffic between your clients and the webserver.
Squid can be used as a caching service to SSL requests as well as DNS lookups. It can also provide a wide variety of support to multiple other types of caching protocols, such as ICP, HTCP, CARP, as well as WCCP. Squid is an excellent choice for many types of setups as it provides very granular controls by offering numerous system tools, as well as a monitoring framework using SNMP to provide a solid base for your caching needs.
When selecting a computer system for use as a dedicated Squid caching proxy server, many users ensure it is configured with a large amount of physical memory (RAM) as Squid maintains an in-memory cache for increased performance.
Installing Squid
Let’s start by ensuring our server is up to date:
[root@test ~]# apt-get update
Get:1 http://security.ubuntu.com/ubuntu xenial-security InRelease [109 kB]Hit:2 http://us.archive.ubuntu.com/ubuntu xenial InReleaseHit:3 http://ppa.launchpad.net/libreoffice/ppa/ubuntu xenial InReleaseGet:4 http://us.archive.ubuntu.com/ubuntu xenial-updates InRelease [109 kB]Get:5 http://us.archive.ubuntu.com/ubuntu xenial-backports InRelease [107 kB]Fetched 325 kB in 0s (567 kB/s)Reading package lists... Done
Next, at the terminal prompt, enter the following command to install the Squid server:
[root@test ~]# apt install squid
Reading package lists... DoneBuilding dependency treeReading state information... DoneThe following packages were automatically installed and are no longer required:linux-headers-4.4.0-141 linux-headers-4.4.0-141-generic linux-image-4.4.0-141-genericUse 'apt autoremove' to remove them.
The following additional packages will be installed:
libecap3 squid-common squid-langpack ssl-cert
Suggested packages:
squidclient squid-cgi squid-purge smbclient ufw winbindd openssl-blacklist
The following NEW packages will be installed:
libecap3 squid squid-common squid-langpack ssl-cert
0 upgraded, 5 newly installed, 0 to remove and 64 not upgraded.
Need to get 2,672 kB of archives.
After this operation, 10.9 MB of additional disk space will be used.
Do you want to continue? [Y/n] Y
Fetched 2,672 kB in 0s (6,004 kB/s)
Preconfiguring packages ...
Selecting previously unselected package libecap3:amd64.
(Reading database ... 160684 files and directories currently installed.)
Preparing to unpack .../libecap3_1.0.1-3ubuntu3_amd64.deb ...
Unpacking libecap3:amd64 (1.0.1-3ubuntu3) ...
Selecting previously unselected package squid-langpack.
Preparing to unpack .../squid-langpack_20150704-1_all.deb ...
Unpacking squid-langpack (20150704-1) ...
Selecting previously unselected package squid-common.
Preparing to unpack .../squid-common_3.5.12-1ubuntu7.6_all.deb ...
Unpacking squid-common (3.5.12-1ubuntu7.6) ...
Selecting previously unselected package ssl-cert.
Preparing to unpack .../ssl-cert_1.0.37_all.deb ...
Unpacking ssl-cert (1.0.37) ...
Selecting previously unselected package squid.
Preparing to unpack .../squid_3.5.12-1ubuntu7.6_amd64.deb ...
Unpacking squid (3.5.12-1ubuntu7.6) ...
Processing triggers for libc-bin (2.23-0ubuntu10) ...
Processing triggers for systemd (229-4ubuntu21.16) ...
Processing triggers for ureadahead (0.100.0-19) ...
Setting up libecap3:amd64 (1.0.1-3ubuntu3) ...
Setting up squid-langpack (20150704-1) ...
Setting up squid-common (3.5.12-1ubuntu7.6) ...
Setting up ssl-cert (1.0.37) ...
Setting up squid (3.5.12-1ubuntu7.6) ...
Skipping profile in /etc/apparmor.d/disable: usr.sbin.squid
Processing triggers for libc-bin (2.23-0ubuntu10) ...
Processing triggers for systemd (229-4ubuntu21.16) ...
Processing triggers for ureadahead (0.100.0-19) ...That’s it! The installation is complete!
Configuring Squid
The default Squid configuration file is located in the ‘/etc/squid/ directory, and the main configuration file is called “squid.conf”. This file contains the bulk of the configuration directives that can be modified to change the behavior of Squid. The lines that begin with a “#”, are commented out or not read by the file. These comments are provided to explain what the related configuration settings mean.
To edit the configuration file, let’s start by taking a backup of the original file, in case we need to revert any changes if something goes wrong or use it to compare the new file configurations.
[root@test ~]# cp /etc/squid/squid.conf /etc/squid/squid.conf.bakChange Squid’s Default Listening Port
Next, the Squid proxy servers default port is 3128. You can change or modify this setting to suit your needs should you wish to modify the port for a specific reason or necessity. To change the default Squid port, we will need to edit the Squid configuration file and change the “http_port” value (on line 1599) to a new port number.
[root@test ~]# vim /etc/squid/squid.conf
http_port 2946(Keep the file open for now…)
Change Squid’s Default HTTP Access Port
Next, to allow external access to the HTTP proxy server from all IP addresses, we need to edit the “http_access” directives. By default, the HTTP proxy server will not allow access to anyone at all unless we explicitly allow it!
Caution!: Multiple settings mention http_access. We want to modify the last entry.
1164 # Deny requests to certain unsafe ports
1165 http_access deny !Safe_ports
...
1167 # Deny CONNECT to other than secure SSL ports
1168 http_access deny CONNECT !SSL_ports
...
1170 # Only allow cachemgr access from localhost
1171 http_access allow localhost manager
1172 http_access deny manager
...
1186 #http_access allow localnet
1187 http_access allow localhost
...
1189 # And finally deny all other access to this proxy
1190 http_access deny all
# > change to "allow all" <Now, let’s save and close the configuration file using vim’s :wq command.
Define the Default NIC Card Squid Listens On
If you would like Squid to listen on a specific NIC (in a server with multiple NIC cards), you can update the configuration file with the NIC’s IP address that Squid will listen on.
For example, we can change it to an internal IP of 10.1.1.5:3128
Define Who Can Access the Proxy Server
Next, we’ll setup who is allowed access to our Squid proxy. Locate the http_access section (which should begin around line 1860) and uncomment the following two lines:#acl our_networks src 10.1.1.0/16 10.1.2.0/16
#http_access allow our_networks
-- VVV change to VVV --
acl our_networks src 10.1.1.0/16 10.1.2.0/16
http_access allow our_networks
You will need to modify the IP ranges (10.1.1.0/16 10.1.2.0/16) to your own internal IP’s to match what your network uses unless you have several subnets you can use. (Netmasks are further explained here.)
Define the Hours that are Available to Access the Proxy
You can literally control the hours of access to the proxy server! The ACL section starts about line 673:671 # noneTo set this up, let’s add this info to the bottom of the ACL section of the /etc/squid/squid.conf file:
672
673 # TAG: acl
674 # Defining an Access List
675 #
acl liquidweb src 10.1.10.0/24Granted, this is an example using Liquid Web as the business name, but you can use any name.
acl liquidweb time M T W T F 9:00-17:00
Other ACL Options Include:
***** ACL TYPES AVAILABLE *****
711 #
712 # acl aclname src ip-address/mask ... # clients IP address [fast]
713 # acl aclname src addr1-addr2/mask ... # range of addresses [fast]
714 # acl aclname dst [-n] ip-address/mask ... # URL host's IP address [slow]
715 # acl aclname localip ip-address/mask ... # IP address the client connected to [fast]
717 # acl aclname arp mac-address ... (xx:xx:xx:xx:xx:xx notation)
...
730 # acl aclname srcdomain .foo.com ...
731 # # reverse lookup, from client IP [slow]
732 # acl aclname dstdomain [-n] .foo.com ...
733 # # Destination server from URL [fast]
734 # acl aclname srcdom_regex [-i] \.foo\.com ...
735 # # regex matching client name [slow]
736 # acl aclname dstdom_regex [-n] [-i] \.foo\.com …
…
… (all the way down to line 989)
…
968 # Example rule allowing access from your local networks.
969 # Adapt to list your (internal) IP networks from where browsing
970 # should be allowed
971 #acl localnet src 10.0.0.0/8 # RFC1918 possible internal network
972 #acl localnet src 172.16.0.0/12 # RFC1918 possible internal network
973 #acl localnet src 192.168.0.0/16 # RFC1918 possible internal network
974 #acl localnet src fc00::/7 # RFC 4193 local private network range
975 #acl localnet src fe80::/10 # RFC 4291 link-local (directly plugged) machines
976
977 acl SSL_ports port 443
978 acl Safe_ports port 80 # http
979 acl Safe_ports port 21 # ftp
980 acl Safe_ports port 443 # https
981 acl Safe_ports port 70 # gopher
982 acl Safe_ports port 210 # wais
983 acl Safe_ports port 1025-65535 # unregistered ports
984 acl Safe_ports port 280 # http-mgmt
985 acl Safe_ports port 488 # gss-http
986 acl Safe_ports port 591 # filemaker
987 acl Safe_ports port 777 # multiling http
988 acl CONNECT method CONNECT
989All Squid Configuration Options
A full accounting of Squid’s available configuration files can be found at these links. (Make sure you plan to take some time because there is a lot of info there)
Restart Squid
After making those changes, let’s restart the Squid service to reload the configuration file.
[root@test ~]# systemctl restart squid.serviceOther Important File Locations for Squid

Even More Information about Squid
How Can We Help?
Our Most Helpful Humans in Hosting can provide clarity and further information about Squid and how it can be utilized in our specific hosting environments, including Ubuntu virtual private servers. Our Support team contains many talented individuals with intimate knowledge of web hosting technologies, especially like those discussed in this article. If you are uncomfortable walking through the steps outlined here, we are just a phone call, chat or ticket away from providing you info to walk you through the process. Let us assist you today!

 Justin Palmer
Justin Palmer