[Updated October 2025]
When cyber threats evolve faster than your defenses, the gap between “protected” and “breached” can be razor thin. That’s where hardware firewalls come in. If you’ve been wondering what separates them from software firewalls or how they actually keep critical systems secure, you’re in the right place.
Next-Gen firewall & VPN
Get the peace of mind that comes with improved security and risk reduction
Key points:
- A hardware firewall is a dedicated physical device that filters all network traffic before it reaches your servers, protecting your entire network—not just individual devices.
- It offers enterprise-grade protection with features like default traffic rules, granular port control, and managed configuration support, freeing up server resources.
- Hardware firewalls outperform software firewalls in scalability, performance, and centralized protection, though they require expert setup and higher upfront cost.
- Top options like the Palo Alto PA-440, Cisco FPR 2110, and Fortinet FortiGate deliver advanced, next-generation security ideal for multi-server or compliance-driven environments.
What is a hardware firewall?
A hardware firewall is a physical device similar to a server that filters traffic to a computer. Instead of plugging the network cable into the server, it is connected to the firewall, positioning the firewall between the uplink and the computer.
Like a standard computer with a processor, memory, and sophisticated software, this device also employs powerful networking components (hardware and software) and forces all traffic traversing that connection to be inspected by configurable rulesets which grant or deny access accordingly.
How does a hardware firewall work?
Every hardware firewall is set up differently, depending on your configuration. The firewall is situated outside your server and is connected directly to your uplink.
If this is a new setup, the firewall is then connected to your server. If this is a new setup to a production server, a maintenance window would be scheduled to handle the physical connection.
Once the connection to the server is established, all traffic to and from the server goes through the firewall, forcing it to pass inspection. This gives you granular control over the type of traffic you’re receiving, which is incredibly important in order to keep your device protected from malware.
Why do you need a hardware firewall?
A hardware firewall provides enterprise-grade protection, centralized control, and stronger performance than software firewalls alone.
Network protection
A hardware firewall is used to protect the entire network, along with incoming and outgoing traffic. It gives network administrators the ability to control the way the network is being used.
Furthermore, a hardware-based firewall can protect other network devices like scanners that don’t have integrated firewalls.
Integration
A hardware firewall easily integrates with other forms of security. In most cases, physical firewalls come with supplementary security features like a virtual private network (VPN). Using a firewall with a VPN connection allows you to grant secure access to the people who need it anywhere there’s a stable Internet connection.
Autonomy
Hardware firewalls come with 24/7 protection built in, so you don’t have to worry about updates and unexpected crashes.
Resources
A hardware firewall protects the whole network. There is no need to install it separately on every device, which saves a great amount of time and resources.
Advantages and disadvantages of a hardware firewall
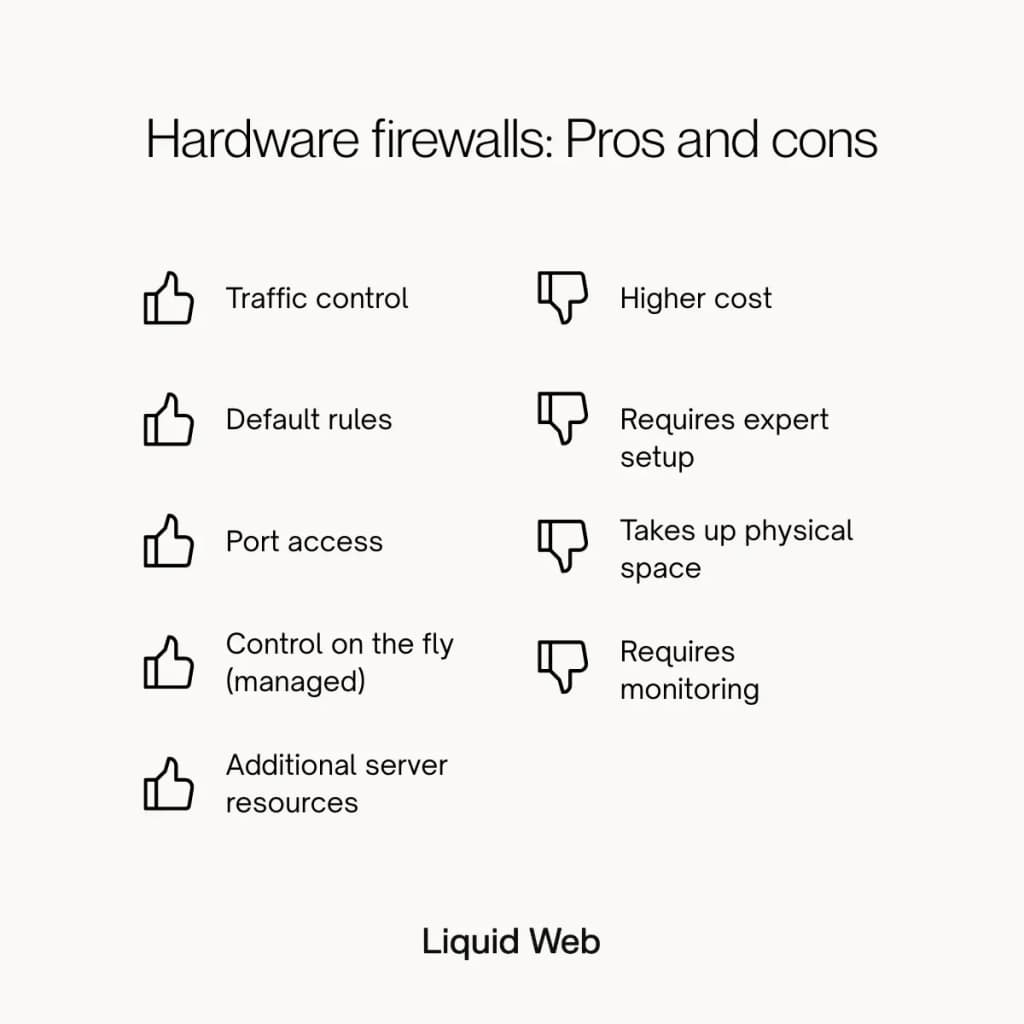
Five advantages of a hardware firewall
Here are the five advantages of a hardware firewall:
1. Traffic control
A hardware firewall acts as a smart gatekeeper, inspecting every packet that enters or leaves your network. It decides which traffic should pass through and which should be blocked, ensuring only legitimate requests ever reach your servers. This keeps your infrastructure efficient, compliant, and protected from unauthorized access.
2. Default rules
Hardware firewalls come with a configurable list of default rules that define how traffic behaves by default, even before custom policies are added. These baseline protections filter out known threats, enforce best practices, and provide immediate security coverage from the moment the device is deployed.
3. Port access
A hardware firewall grants granular control to tailor rules with options like allowing all traffic to your website or ensuring only you and your developer can access SSH ports or Remote Desktop Protocol (RDP).
4. Control on the fly (managed)
With a fully managed hardware firewall, you get access to expert network engineers who can adjust configurations, create new rules, or troubleshoot issues in real time. This flexibility lets you adapt instantly to changing traffic patterns or emerging threats without interrupting operations.
5. Additional server resources
A hardware firewall gives you access to additional server resources that would otherwise be utilized since it is a completely separate device from your server. You can even disable the software firewalls from your server and rely completely on the hardware firewall, freeing up valuable memory and processing power for the functions and services that your business needs to continue being successful.
4 challenges of a hardware firewall
Here are a few considerations to be made if you are thinking about using a hardware firewall:
1. Higher cost
Hardware firewalls typically cost more than software-based solutions because they involve specialized hardware and advanced network capabilities. You can offset this expense by choosing a managed hosting provider that includes firewall hardware and monitoring as part of a bundled security package.
2. Requires expert setup
Installing and configuring a hardware firewall demands technical expertise to ensure optimal performance and avoid misconfigurations. Partnering with a managed hosting provider or experienced network team ensures proper deployment and ongoing management without in-house complexity.
3. Takes up physical space
Because hardware firewalls are separate physical devices, they require rack space, power, and cabling in your infrastructure. While unavoidable, colocating your firewall in a managed data center or hosting environment keeps it maintained without occupying your on-site resources.
4. Requires monitoring
Even though hardware firewalls provide continuous protection, they need regular monitoring, firmware updates, and policy reviews to stay effective. Managed firewall services ease this burden by handling updates, analyzing logs, and responding to threats in real time.
Hardware firewall examples
The firewall market allows you to choose the firewall based on your needs and budget. We have collected some of the most popular firewall solutions in the list below:
Palo Alto PA-440
The Palo Alto PA-440 brings enterprise-grade security to small and mid-sized businesses, offering advanced protection in a compact next-gen firewall. Built on Palo Alto Networks’ powerful PAN-OS platform, the PA-440 provides deep visibility into traffic, users, and applications, enabling intelligent threat prevention without sacrificing performance.
Its hardware-accelerated architecture supports SSL decryption, sandboxing, and advanced malware analysis (features typically found only in higher-end models ), making it ideal for organizations that need robust defense in a smaller footprint.
Key Features:
- Zero Trust Network Security with App-ID and User-ID technologies
- Integrated machine learning for real-time threat prevention
- Centralized management through Panorama
- Compact form factor optimized for branch offices and small enterprises
Learn more: “Why we picked the Palo Alto PA-440” →
Bitdefender BOX
Bitdefender’s technology has pioneered breakthrough innovations in antimalware, behavioral analytics, and artificial intelligence.
The Bitdefender BOX comes bundled with a Bitdefender Total Security subscription which allows you to monitor inbound traffic – defending your network against potential hacks or intrusions – as well as outgoing traffic, blocking things like requests to known malicious sites or sending sensitive data (such as a password) over an insecure connection.
Key Features:
- Unlimited protection and support
- Parental control
- Cross-platform security
Checkpoint
The Checkpoint solutions secure customers from Gen V cyber attacks by catching malware, ransomware, and other sorts of attacks at an industry-leading rate. Because these attacks are quick, multi-vectored, and extremely harmful, it’s critical to provide an extra layer of security in addition to real-time threat prevention.
Check Point firewall protects virtual instances, cloud deployments, endpoints, remote offices, and mobile devices with a single architecture and powerful threat prevention technologies in real time.
Key Features:
- Unified management platform
- Ultra-scalable protection against Gen V cyber attacks
- Remote access VPN
Fortinet
Fortinet is the only security company that develops and manufactures custom security processing unit technology in order to provide the best performance and cost value in the industry. Fortinet’s firewall provides industry-leading enterprise security for any edge at any scale with full visibility and threat protection.
Key Features:
- Ultra-fast security, end to end
- Operational efficiency and automated workflows
- Real-time defense with FortiGuard Services
Netgear ProSAFE
Netgear is known as an enterprise cybersecurity service provider that offers storage, network, and security solutions at affordable prices. This firewall router comes with a stateful packet inspection firewall, Denial of Service protection, and intrusion detection.
Key Features:
- Real-time alerts
- 8 simultaneous VPN tunnels
- Easy-to-use browser-based setup
Which is better: Hardware firewalls vs software firewalls
Both types of security firewalls are used to provide a secure connection between the local network and the Internet. The choice is mainly based on the user’s needs and financial capabilities.
Here are some of the major differences between software and hardware firewalls:
| Feature | Hardware firewall | Software firewall |
| Deployment | A physical device placed between your network and the internet | Installed directly on a computer or server |
| Scope of protection | Protects the entire network from external threats | Protects individual devices only |
| Performance impact | Offloads processing from endpoints, keeping performance high | Uses local system resources, which can slow devices |
| Configuration & management | Managed per device, with optional centralized management | Easier to configure; managed per device |
| Traffic monitoring | Monitors incoming and outgoing traffic. | Monitors both incoming and outgoing traffic on a device |
| Scalability | Scales easily for large or multi-server environments | Limited scalability; must be installed on each device |
| Cost | Higher upfront and maintenance cost | Lower cost, often bundled with operating systems |
| Physical requirements | Requires rack space, power, and cabling | No additional hardware required |
| Security strength | Provides enterprise-grade, always-on protection with low latency | Effective for personal or small network use but less comprehensive |
| Best use case | Businesses managing multiple servers, sensitive data, or compliance needs | Individual users, remote workers, or small offices needing endpoint protection |
Why choose a hardware firewall
Businesses are more likely to require a hardware firewall. It provides protection for your entire network through a single, standalone physical device, which means it also does not use server resources.
However, while it does not require updates like software does, it does need a dedicated specialist to install and manage. Also, a hardware firewall requires monitoring and has a higher cost than using a software firewall solution.
Why choose a software firewall
A software firewall is more appropriate for personal use, although there are certainly business applications. Software firewalls protect a single device, so if you plan to use software firewalls to protect your entire network, it will need to be installed on each device.
It is easier to install and less expensive than a hardware firewall and includes automatic monitoring. However, regular manual updates are necessary to keep protected from the latest threats, and it does use server resources since it is not on a standalone device.
Hardware firewall FAQ
Get secure with a hardware firewall at Liquid Web today
Liquid Web stocks several versions of hardware firewall devices. These devices are powerful enough to handle traffic from multiple servers, including dedicated servers and bare metal servers. We also employ a full staff of dedicated networking professionals 24/7/365 who can manage and maintain your fully managed networking infrastructure.
Palo Alto PA-440
For organizations that need advanced protection in a compact package, the Palo Alto PA-440 delivers enterprise-grade security with next-generation capabilities. Powered by PAN-OS and backed by Palo Alto’s machine learning threat intelligence, it provides real-time visibility into applications, users, and content. Its next-generation firewall (NGFW) architecture operates at Layer 7, enabling deep packet inspection and application-aware control that goes far beyond traditional port-based filtering.
Cisco FPR 2110
Cisco FPR is a next-generation firewall line that expands the features of the ASA model. FPR’s automated updates mechanism will enhance consistent network visibility. If you are looking for a top-notch security solution, you should try our advanced malware protection to simultaneously protect your network and endpoints from online threats such as malicious firmware.
Contact us now to get started with a new firewall.


 Vanessa Stephens
Vanessa Stephens