Tag: Code
A Guide to Writing Comments in Python
What is a Comment?
In simple terms, a comment is an entry added to the source code to allow a deeper understanding of the logic behind why the code was written the way it was. In Python, the hash (#), number sign, or pound symbol is required before every inline comment. This symbol allows the Python interpreter or compiler to ignore the pursuant text.
What is PHP and What is it Used For?
What is PHP?
PHP is a widely-used open source, general-purpose, server-side scripting language. It was released in 1995 by Rasmus Lerdorf and has since evolved into one of the most popular programming languages with a large community of developers worldwide. The abbreviation PHP originally stood for Personal Home Page but has since been changed to PHP: Hypertext Preprocessor.
Azure DevOps and CI/CD
Azure DevOps is a set of tools and services provided by Microsoft that helps developers and teams collaborate and automate the process of building, testing, and deploying software. One of the key features of Azure DevOps is its ability to support continuous integration and continuous delivery (CI/CD), a software development practice that helps teams deliver code changes more frequently and with higher quality.
What is a GitHub gist?
About GitHub gists
One of GitHub's most innovative features is Gist, which lets you store and distribute code snippets without setting up a full-fledged repository. Code strings, bash scripts, markdown, text files, and other small pieces of data are all acceptable alternatives to just code snippets. It can be used to quickly distribute a piece of code to others for anything like a demonstration, a how-to, or any solution without setting up a standard repository. Additionally, you can use it to embed elsewhere or on your website.
A Beginner’s Guide to Chef on CentOS 8
What is Chef?

Chef is an open-source configuration management DevOps tool used for configuration and management of multiple systems in infrastructure. Using Chef, we can use so-called recipes and cookbooks to automate and speed up managing multiple systems in our environment. By using Chef, we can adjust every system in our environment to our desired state, which we defined using the code in recipes. In the process, code is continuously tested and deployed using Chef.
How to Install Jenkins on Ubuntu 20.04
How to Install Jenkins on CentOS 8
What is Jenkins?
Jenkins is an open-source software written in Java and Scala. This software allows users the ability to automate almost any task and, it saves significant time that can be better utilized addressing other issues. When automating tasks with Jenkins, users can optimize their workflow by quickly automating the jobs that servers cannot do themselves. In this tutorial, we will learn how to install Jenkins on CentOS 8. We will also explore what its purpose is and share several benefits that Jenkins offers. We will then configure it to run on our CentOS 8 server.
What is Infrastructure as Code? (IaC)
Introduction: What is IaC?
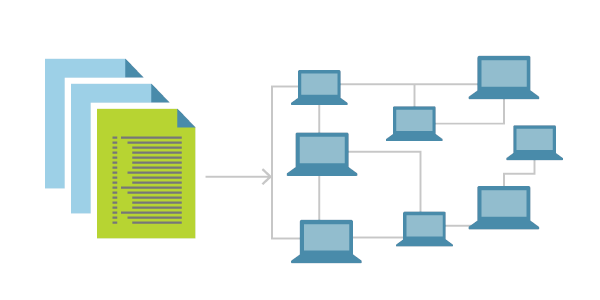
Today we will become acquainted with a concept known as Infrastructure as Code. The idea of Infrastructure as Code is becoming more and more popular today. IaC is a method used to manage and provision a data center via defined machine-readable files instead of physical hardware configuration or other interactive configuration tools. This article will share what it is used for, why it is important, and why businesses strive to utilize this platform to achieve a desired set of results. It is essential to understand that we will consider both the theoretical and practical parts of IaC.
How to Implement Zero Trust Security in 5 Steps
Zero Trust security is the concept, methodology, and threat model that assumes no user, system, or service operating within a secured internal environment should be automatically trusted. It put forward that every interaction must be verified when trying to connect to a system before being granted access. This concept uses micro-segmentation, and granular edge controls based on user rights, application access levels, service usage, and relation to the location to determine whether to trust a user, machine, or application seeking to access a specific part of an organization.
How Was My Website Compromised?
In this tutorial, we will look at several methods that are used to compromise a website. In today's world, websites use multiple procedures that represent the core functions of a modern business. Whether you have an eCommerce site or a business card site, a website is essential for driving business growth. We can safely state that a website is a unique image of your respective business.
Our Sales and Support teams are available 24 hours by phone or e-mail to assist.

