(On Unmanaged/Core Managed Servers)
What Is CSF?
In this article, we will provide an in-depth explanation of how to set up and customize the messenger feature in CSF on an unmanaged or core managed server. Let’s begin by defining exactly what CSF or ConfigServer Firewall is and what it does.

CSF is an open-source “Stateful Packet Inspection (or SPI) firewall, Login/Intrusion Detection and Security application for Linux servers.” It is a “secure, straightforward, platform that is flexible and easy to configure with extra checks included to ensure smooth operation. CSF can be used on any generic Linux OS. The CSF installation includes preconfigured configurations and control panel UI’s for cPanel, DirectAdmin, and Webmin.”
Additionally, CSF is paired with LFD (the Login Failure Daemon).
The LFD process “runs continuously and will periodically (every X seconds) scan the latest log file entries for login attempts against your server that continually fail within a short period of time. Such attempts are often called “Brute-force attacks” and the daemon process responds quickly to such patterns and blocks offending IP’s quickly. Other similar products run every x minutes via cron and as such, often miss break-in attempts until after they’ve finished, Our daemon eliminates such long waits and makes it much more effective at performing its task.”
configserver.com
What Is CSF Messenger?
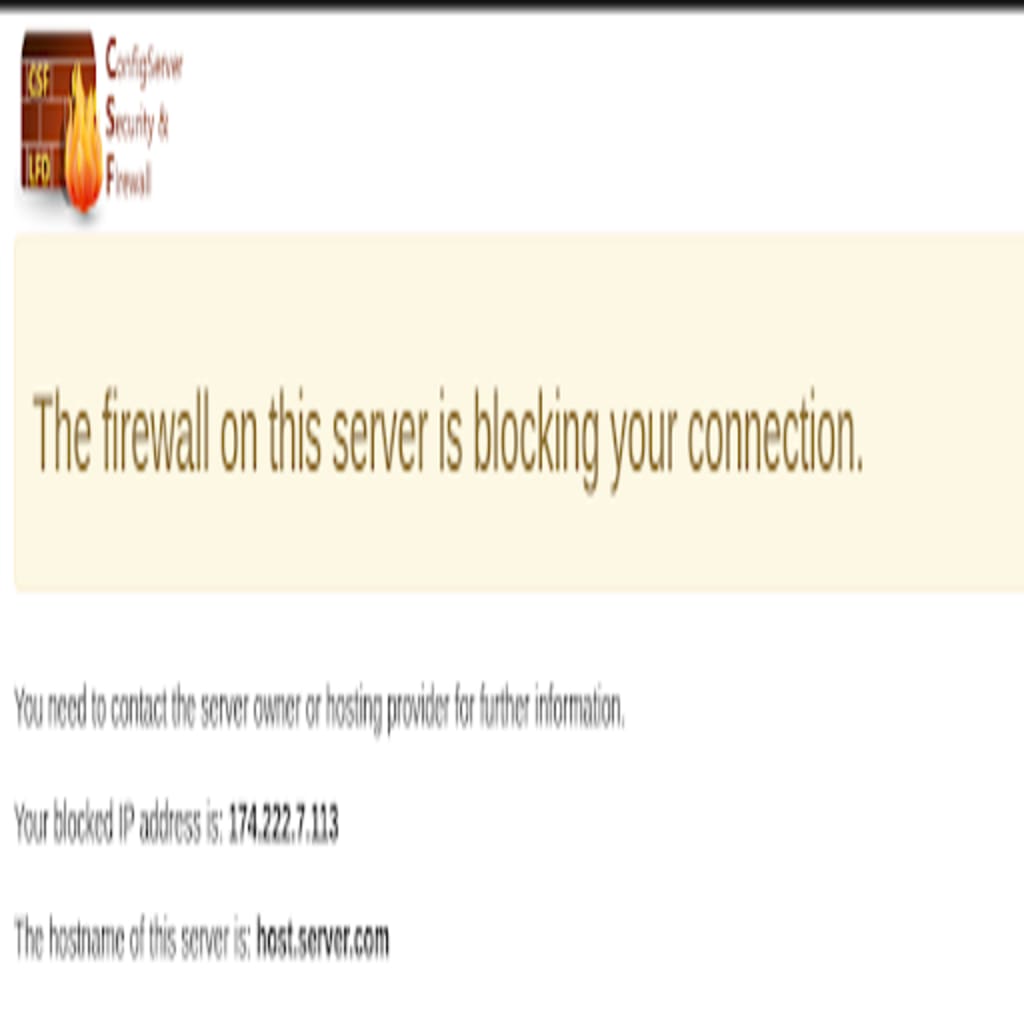
The CSF messenger is a feature which displays a specific warning page to a user if they are blocked in the firewall similar to the one seen below, CSF also provides the user with the blocked IP address, so that when they contact the server owner or administrator to have the IP unblocked, they will have all the information they need to provide to whitelist the IP if appropriate.

This feature is very pliant, especially if there are clients who frequently get locked out of a site due to being blocked in the firewall. The majority of those users may presume that there is something wrong with the server or the site and assume it is down for everyone, when in fact, it is simply inaccessible to them. This provides users with the peace of mind in that they know that they are just blocked in the firewall, from which they can easily be removed. This attribute also has the potential of saving lost business by providing an extra layer of protection from would-be malicious individuals or attackers.
ReCaptcha
You can further customize this aspect by enabling the reCAPTCHA option. The reCAPTCHA functionality is a CAPTCHA-like method designed to verify that the computer user is a human being. If the user successfully finishes the captcha challenge, they can unblock themselves. We have included the directions to implement this option below.
Note: Please keep in mind that if a malicious person is blocked, they will also have the option to become unblocked through the successful completion of the captcha challenge. Also, when the ReCaptcha option is enabled, by default, you also receive an email alert when someone successfully unblocks their IP address. Furthermore, the server must also be running Apache v2.4 and using cPanel’s EasyApache v4. The Messenger User MUST also have a specific directory Structure that the script provides.
Implementation
Implementation via Command line on an Unmanaged/Core managed server.
This single line command will:
- backup CSF’s configuration file
- update CSF to the latest version
- make the necessary configuration file changes
- then restart the CSF services to enable the messenger feature
(You will need to log in as root or have sudo access)
root@host:~# cp /etc/csf/csf.conf{,.backup} && csf -u && sed -i 's/MESSENGER = "0"/MESSENGER = "1"/g' /etc/csf/csf.conf ; sed -i 's/MESSENGERV2 = "0"/MESSENGERV2 = "1"/g' /etc/csf/csf.conf ; sed -i 's/MESSENGER_HTTPS_IN = ""/MESSENGER_HTTPS_IN = "443"/g' /etc/csf/csf.conf ; useradd csf -s /bin/false ; csf -raTo test this feature, we recommend using a different device that is NOT connected to the same network as the PC you are setting this up on. Once you are online with your other device operating in a different network, you will need to retrieve your public IP. You can do this by simply going to a reliable IP address checker. Once you have your IP address, you’ll need to add it to the deny list in CSF
(Using my test IP 174.222.7.113 in the example below)
root@host:~# csf -d 174.222.7.113If you don’t have an extra device or means to test with an alternative IP you can block yourself temporarily for the next X number seconds. In the example below, the IP will be temporarily blocked for 30 seconds.
root@host:~# csf -td 174.222.7.113 30Once blocked, try to access your domain, you will see a page similar to the following one.
To unblock the alternative IP, use this command.
root@host:~# csf -dr 174.222.7.113Enable reCAPTCHA Option — Command line on Non-cPanel
Note: This process REQUIRES a Gmail account to proceed.
First, you will need to create the reCAPTCHA Site key & Secret key. To do this, go to Google’s recaptcha site, and then click on the “Admin Console” button on the top right of the page.

Once logged in to your Gmail account, you will be directed to a page with the title “Register a new site.” For the site label, you can put whatever entry you would like, in order to reference the keys you’re about to create e.g. “CSF Messenger”. Then, select the type of reCAPTCHA method you would like to implement. We prefer the “reCAPTCHA v2 Checkbox” option, but either one of them will work. For the domain entry, type in the hostname of your server
Make sure to click on the plus sign the left of the domain you typed to add it. Then, check the box next to accept TOS (if you agree with them), and hit submit.

The subsequent page will display the Site key in the very first box and the Secret key in the second box. You will need to keep those keys handy because you will need them to configure the reCAPTCHA option within CSF next.

Next, to make the following step easier, run the command noted below. It will ask you for the Site Key and Secret Key you received above and then make the needed changes for you, and finally, it will restart CSF to implement the changes. If by chance you make a mistake, simply hit ‘ctrl+c’ to break/stop the command, or you can wait until CSF is finished restarting and then run the command again.
root@host:~# cat echo "What is the Site Key?:" ; read skey ; echo "What is the Secret Key?:" ; read secret ; sed -i '/RECAPTCHA_SITEKEY = "/c\RECAPTCHA_SITEKEY = "'$skey'"' /etc/csf/csf.conf ; sed -i '/RECAPTCHA_SECRET = "/c\RECAPTCHA_SECRET = "'$secret'"' /etc/csf/csf.conf ; csf -raNext, we will need to replace CSF Messenger’s default index.php with the code modified with the reCAPTCHA information. To accomplish this, run the following command.
root@host:~# cat /etc/csf/messenger/index.recaptcha.php > /home/csf/public_html/index.phpFinally, follow the same steps as above to set up a firewall test block of your IP to try out the reCAPTCHA auto-unblock feature.
Note: The unblock feature can take a few seconds to complete. In our testing, we had to wait as long as 10 seconds sometimes before the IP was unblocked. (The average wait time for us was less than 3 seconds on average).
If you would like to customize the look, functionality, or info on the block page the files are located in; /home/csf/public_html/, specifically /home/csf/public_html/index.php.
We’d Love For You To Join Us!
Are you constantly on the lookout for new security features to further enhance the security of your site or server? If so, Liquid Web has the experts standing by to assist you in implementing features like this and many others available on our hosting products.
Open a chat or ticket with us to speak with one of our experienced support team members to learn more ways to secure your site or server!

 Scott Bixby
Scott Bixby