Data privacy for remote workers is essential. It always has been. But now, more than ever, it is dominating the cybersecurity strategies of all businesses.
Between 2019 and 2021, the number of people primarily working from home tripled from roughly 9 million to 27.6 million. This is according to the new 2021 American Community Survey (ACS) 1-year estimates released by the U.S. Census Bureau. As more businesses shift towards a remote work model, that number is only expected to go up.
But, along with the increase in remote workers, the levels of cybercrime have also risen. This begs the question: How do we protect the privacy of remote workers and company data?
There were 4,145 publicly disclosed breaches that exposed over 22 billion records in 2021, illustrating just how important it is to ensure that data remains safe and out of the hands of hackers.
So, with that in mind, let’s take a look at five tips you should follow to ensure your data privacy.
1. Store Your Passwords in an Encrypted Vault
Passwords protect every online account, but just how safe are they? The truth is that most of the passwords we use are not secure. The reason why: entropy.
What Is Entropy?
Entropy is the measurement of the randomness or diversity of a data-generating function.
Passwords with high entropy are completely random and have no meaningful patterns, making them almost impossible to crack. Unfortunately, the average person can’t memorize complex, random passwords. This means that human-generated passwords tend to only be about 40 bits of entropy. To put this into perspective, a password with 128 bits of entropy is virtually unbreakable; therefore, 40 bits give hackers a much higher possibility to predict the value.
Poor Password Practices
The average person now has over 100 passwords. The sheer volume that we have to remember makes us even more prone to unsafe password practices, such as recycling old passwords or using the same ones for multiple accounts.
These poor password practices compound remote working risks. Employees often opt for convenience over security, saving sensitive login credentials using unsecured methods, including spreadsheets and notes of paper. Some employees also share passwords via email. Hackers are well aware of these cyber hygiene pitfalls and exploit them regularly for financial gain. No country or business is immune, and exposure to cybercrime is rife.
How Password Vaults Can Help
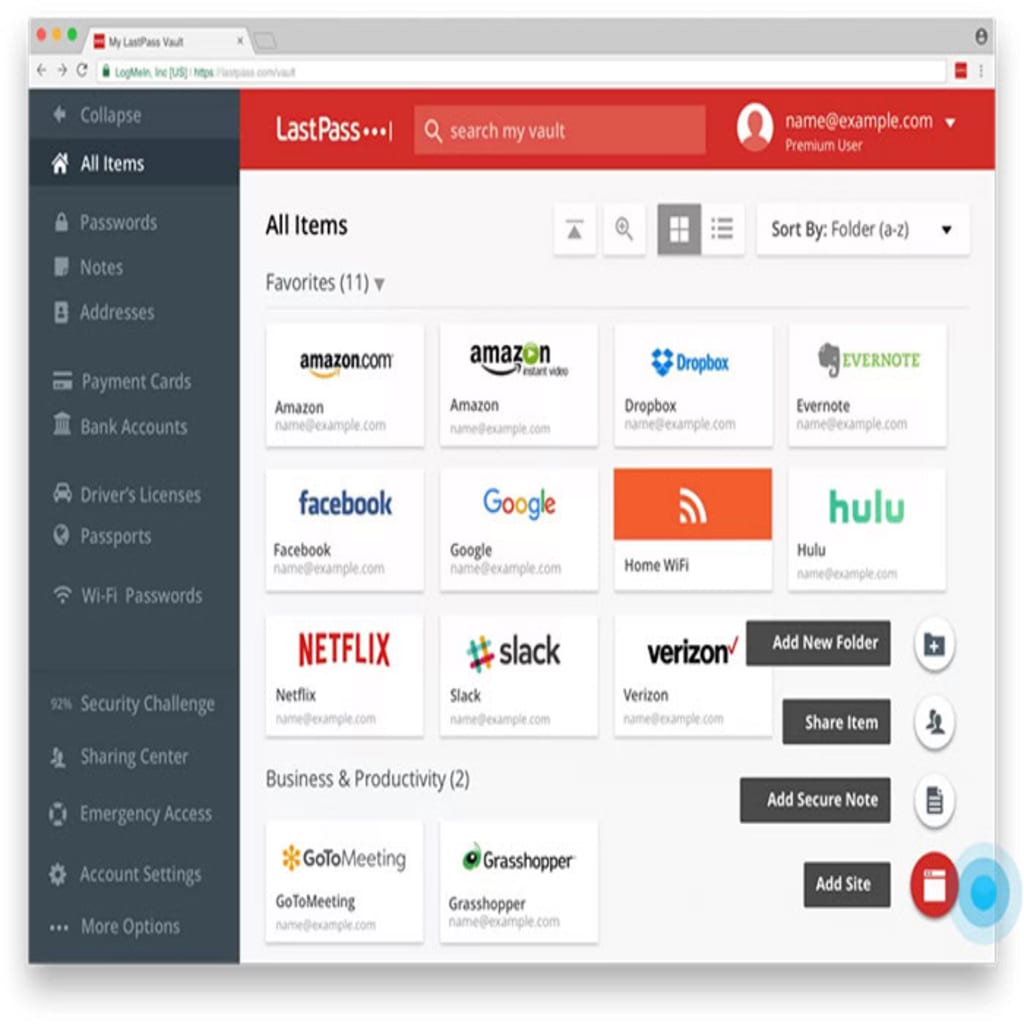
The most effective way to protect credentials from malicious hackers is to store them in an encrypted password vault, otherwise known as a password manager.
Password managers facilitate security and convenience by enabling businesses to store an unlimited number of passwords in an encrypted vault. Therefore, your remote team no longer needs to remember long complex passwords. Instead, they can rely on the software to automatically fill in the login credentials whenever they need them.
The zero-knowledge security models employed by password managers also lend themselves to full data privacy where the software never sees or stores your unencrypted passwords on their servers. If a hacker managed to get in, they would see only streams of meaningless, encrypted code.
Ultimately, password managers enable remote workers to save unique passwords with high levels of entropy for each account in securely encrypted vaults to strengthen the security of business accounts. They can also play a key role in ensuring complete data privacy via single sign-on solutions that make business-critical accounts accessible in one convenient portal. Remote workers simply need to log into the vault and click on the account they need access to. The password manager will log them in automatically without ever displaying the login credentials.
2. Shield Your Data From Prying Eyes
One of the main challenges that IT staff face with remote workers is providing them with a way of accessing company resources while maintaining security and optimal network speeds. This is where a virtual private network (VPN) comes into play.
VPNs form the basic backbone of remote working security and provide workers with a secure method to connect to company resources like shared files. More than 400 million businesses and consumers are already making use of VPN connections, and this number continues to grow as more people start working from home. Working remotely without using a VPN poses a serious security risk since it’s much easier for hackers to intercept confidential data as it travels between your remote location and the office.
A VPN is like a private tunnel that links your remote location directly with your office, and since this tunnel shields the data that travels in it from view, it is much more difficult for hackers to intercept and steal. Employees working from home can use a VPN to connect to most remote resources, including mail servers, CRM programs and software, and even accounting systems.
It is especially important to use a VPN in cases where remote employees use their computers for both personal and professional computing needs. Employees can often unknowingly download malware-infected files and, in doing so, expose confidential company data.
3. Secure Both Work and Personal Devices
Endpoint security, in its simplest form, refers to securing individual devices that connect to a network, such as laptops and mobile phones.
Enhance your cloud asset security by leveraging additional protection add-ons and endpoint software like antivirus, antimalware, and firewalls. This foundation of defense is essential for any remote worker looking to stay secure.
There’s also a concern about “spying” and security breaches through phones and mobile devices that are used for work. Making sure team members are regularly updating security tools, reviewing app permissions, and monitoring unusual activity are important steps to detect and prevent unauthorized access.
Vigilance Is Key
Because endpoint security solutions are often cloud-based, they can be easily distributed across devices remotely. But suppose you are not able to install the appropriate security software. In that case, it’s best only to use the devices granted to you by your business since these will have already been factored into your company’s IT security network and infrastructure.
Whilst working from home can often make us less vigilant to the threats that we face, it’s worth noting that endpoint devices are second only to servers as the most targeted type of asset in data breaches. Remote workers who choose to use their own devices for both work and personal use can create an avenue for hackers to worm their way into company systems if they do not properly protect those devices. Therefore, remote workers must notify IT teams of the devices they use to access business systems.
Practice Safe Computing
It’s important to remember that endpoint security doesn’t just refer to the likes of antivirus software. It also includes the way that we interact with our devices. In order to reduce security vulnerabilities and the risk posed by hackers, remote workers should adopt safe computing practices, such as avoiding potentially malicious websites and not opening emails that may contain dodgy attachments.
The global endpoint security market is projected to grow from almost $14 billion in 2021 to over $24 billion in 2028. This is an indicator of just how important it is for both corporations and end-users to invest in endpoint security if they have not already done so.
4. Use Encrypted Communication Platforms
Communication is key in every business, and it is even more important in remote working environments.
We often hear of hacked email accounts and the exposure of confidential business communications that seriously affects data privacy. But as businesses increasingly opt for chat-based and online meeting platforms, securing these newly-adopted communication channels becomes evermore important. For this reason, consider using a secure and customizable CPaaS platform to secure your data and get your messages across.
Chat applications facilitate higher levels of productivity, thanks to a more seamless communication method than email. And some also offer data privacy. Secure chat applications encrypt messages before they are sent to the intended receiver. Should a hacker intercept the message, they will not be able to read it, and your information stays private.
The following are some of the best-encrypted messaging applications that will protect your data:
Signal
Signal is an encrypted messaging application that’s free to use and includes an option to limit how long a message will be available on any device. The time interval can be between five seconds and seven days. After which, the message will be deleted from all devices.
Threema
While there is a one-time download fee, Threema’s biggest advantage is that it uses a decentralized server. This means if one server becomes unresponsive, you will still be able to send messages because the app will automatically connect to a working server.
Wire
Wire is not as popular as the other encrypted communication platforms, but your business and personal messages, calls, and files will be protected with end-to-end encryption.
The benefit of these applications is that they are web-based and, therefore, offer cross-platform and device compatibility, making them ideal for remote working where they can be accessed anywhere, anytime.

5. Protect Yourself Beyond Software
Aside from using security software like firewalls and making sure your anti-virus and malware software are up to date before downloading anything, there are a few other things that you can do to keep your data safe.
Log Out Whenever You Leave Your Workspace
It’s important to remember that public spaces are not as safe as the office spaces we’re accustomed to working in. You should never leave your computer unlocked when it’s not in your possession. An unlocked computer is a prime target for hackers, so make sure to log out before you leave.
Do Not Connect to Public Wi-Fi Hotspots
Public Wi-Fi often has little to no security. You should avoid connecting your computer or smartphone to a public network whenever possible to protect yourself from malicious actors. A good alternative to public hotspots may be bringing your own mobile data connection when you have to work outside of your usual workspace. Or, if you have no choice but to connect to a hotspot, use a VPN.
Physically Secure Your Devices
When working in a public space, consider using a physical security device like a Kensington lock to secure your laptop.
Ensure Your Business Documents Are Secure
With more businesses signing documents online and keeping important files in the cloud, you need to ensure their security. Use encrypted e-signature software and strong password protection for your business documents.
Adopt Remote Work Security Best Practices Today
Working from home has become the new norm, and data privacy is essential. To ensure your data is safe and secure as you work remotely, it’s critical to adopt best practices. It may seem like unnecessary extra steps, but with the rising number of remote workers, security should be taken seriously.
By following the simple security steps outlined here and making data privacy your number one priority, you will enhance the safety of your data and be able to work stress-free from the comfort of your home.

 Neil Golden
Neil Golden